
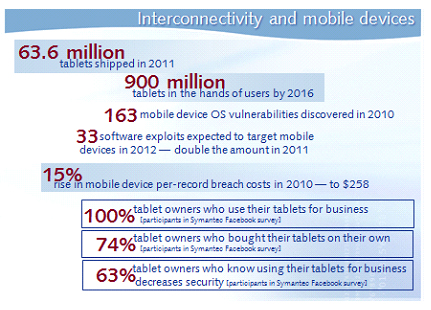
As this infographic shows, expanding interconnectivity between organizations and the fast-accelerating mobility of your employees means your IT infrastructure vulnerabilities are increasing quickly.
What’s more, even one compromised device can be used to tunnel to other connected networks and devices, so it’s easier than ever for bad guys to compromise your IT infrastructure from behind your firewall.
This plays out in other ways, too, including…
- USB malware is gaining momentum — so flash drives and other USB-connected devices can become malware vectors.
- Hackable RFID and radio frequency channels create voicemail vulnerabilities and enable call interception.
- RAM scraping exploits moments when sensitive encrypted data is unencrypted in browsers, smartphones, point-of-sale system memory, etc.
Of course, there’s no stopping the use of mobile devices like smartphones and tablets, no matter what sort of security threats they vector. What you need are tools and techniques that help secure these devices and the infrastructures they interact with.
I recommend mobile device management services, which can secure, monitor, manage, and support up to thousands of devices to troubleshoot them and make sure your compliance policies stick while minimizing downtime and reducing support costs and risks.
Infographic sources:
2010 Annual Study: U.S. Cost of a Data Breach, March 2011, Ponemon Institute/Symantec
Gartner press release, November 15, 2011
Survey Finds an Alarming Gap Between Tablet Usage and Security, September 29, 2011
In 2012, a mobile security minefield, November 28, 2011
Symantec Internet Security Threat Report, April 2011, Symantec

