Cybersecurity Monitoring and Alerting Services
Keeping your network robust, reliable, and secure with IT security monitoring services.
Keeping your network robust, reliable, and secure has never been more important than it is today.
Problems and points of vulnerability can stem from computers, tablets, devices, and phones. These are devices that handle all the demands from databases, email clients, applications, and more. Being able to trust that your company's IT infrastructure is protected and under round-the-clock surveillance with cyber security monitoring solutions is essential.
Quest's 24/7 Cybersecurity Monitoring and Alerting Services covers essential network maintenance. It ensure continual updating, monitoring, and analysis to keep your organization's productivity at optimum levels.
Aggressive cyber attacks are on the rise, and relying on traditional security measures is no longer enough. Cyber attacks are lurking around every corner, ready to strike and cause costly disruptions to your business operations. Cyber security continuous monitoring services offer real-time protection against evolving threats. This gives you peace of mind knowing your data is safe.
Stay one step ahead of cyber threats with continuous IT infrastructure monitoring. Detect and respond to threats before they escalate, protecting your business from potential damage.
Don't wait for a cyber attack to strike, invest in cybersecurity monitoring services from Quest.
Monitoring your company: From endpoints to network and into the cloud.
Quest will monitor your environment in real-time and around the clock. With Quest's expert resources and sophisticated tools employed on your organization's behalf, you can trust in uninterrupted business operations and fast alerts should anything need your attention.
Network security monitoring services are a robust shield that establishes stringent checkpoints on your IT infrastructure. It ensures only authorized information traverses your business’s network. Comprehensive monitoring helps to effectively repels hackers and halt malicious software for the safety of all data in transit. This includes data that moves to the cloud and back to your devices.
Endpoint security protects every access point of each device connected to your network. This includes computers, smartphones, or tablets. The primary objective is to secure each individual device against viruses, malware, and other cyber threats.
Protect your business from the looming threat of cyber attacks with our advanced cyber security monitoring services. By proactive cyber threat monitoring and thwarting potential threats, you can ensure smooth operations and safeguard sensitive data.
Quest’s services help you gain insights into vulnerabilities and strengths, so to make informed decisions on how best to fortify defenses.
Quest offers five categories of Cyber Security Monitoring and Alerting Services.
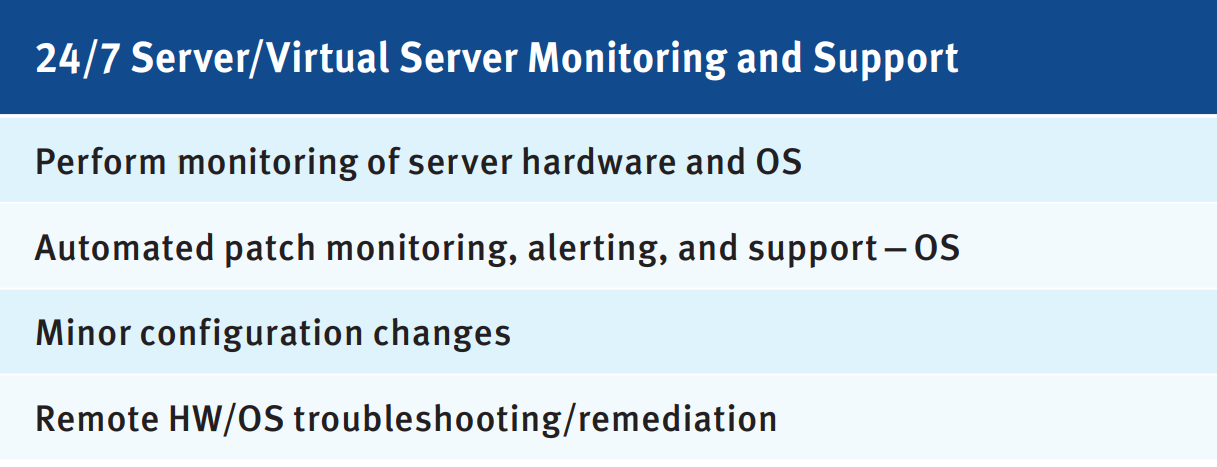
Server/Virtual Server Monitoring and Support
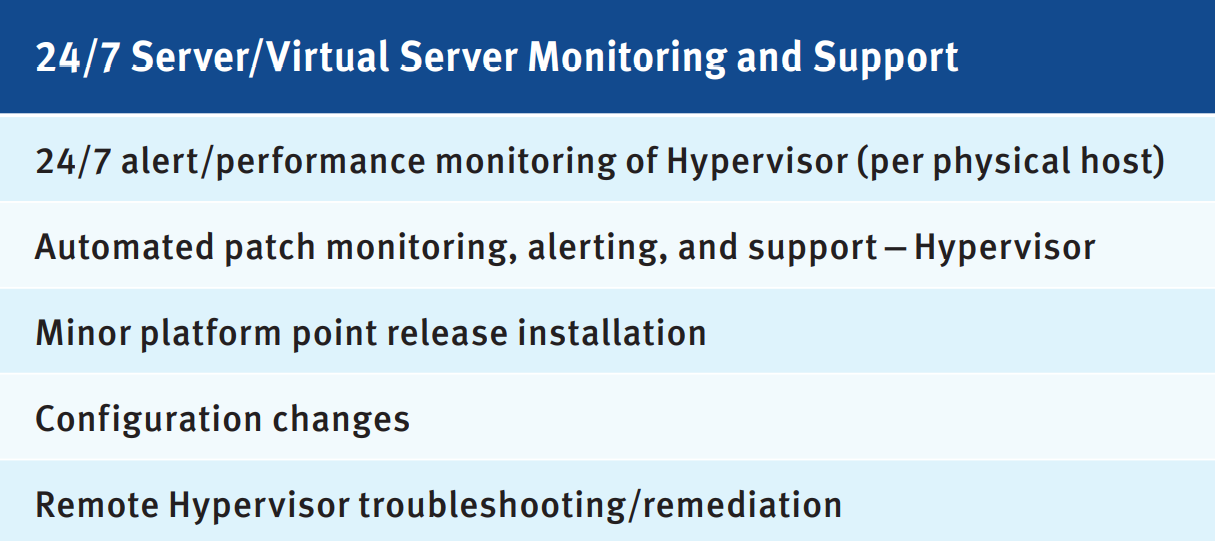
ESX/vCenter Monitoring and Support
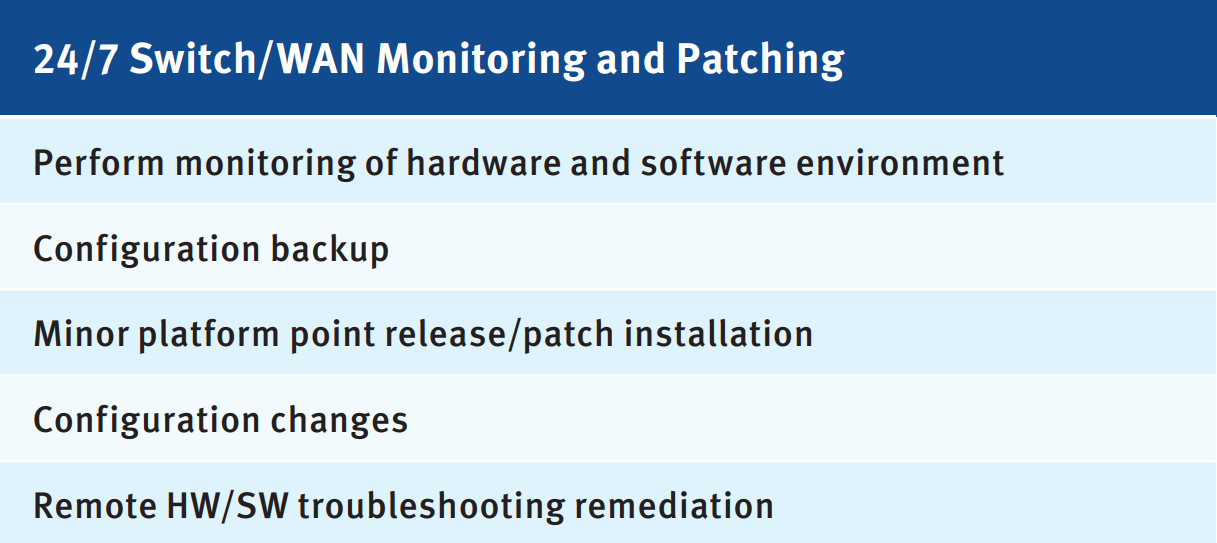
Switch/WAN Monitoring and Patching
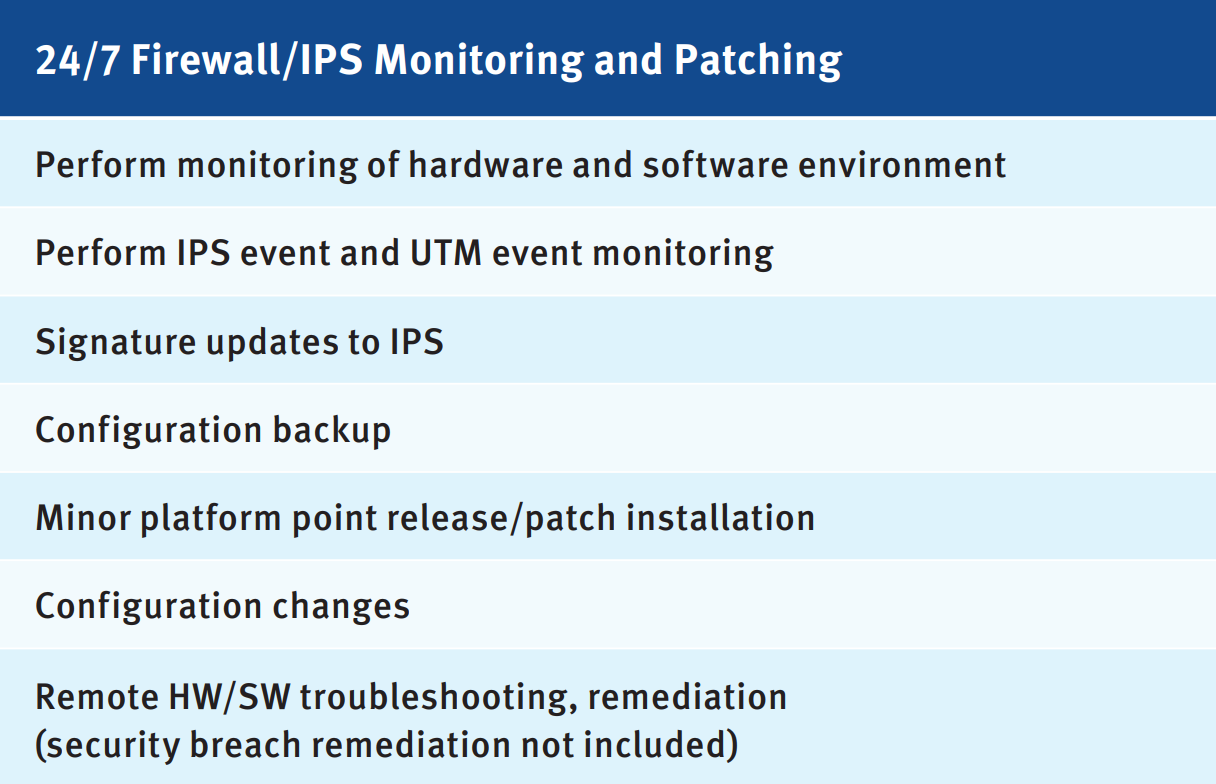
Firewall/IPS Monitoring and Patching
UPS Monitoring and Patching
One data breach could lead to a loss of trust. You don’t want your business data compromised, operations halted, and customers fleeing due to a cyber attack. The consequences are severe, from financial losses to damage to your reputation.
With Quest on the job, you can relax knowing your infrastructure is secure. Our security experts will position your IT resources to help your business realize its financial and strategic objectives. Reinforce your workforce with Quest's cybersecurity expertise and sophisticated tools for network alerting, continuous monitoring for cyber security, and support on your side.

